EFI分区文件结构(仅说明3个必要文件)
(EFI分区)..................此分区必须为Fat32格式,不然UEFI固件将无法识别
|
+--EFI
|--Microsoft
| +--Boot
| |--bootmgfw.efi...一个针对Windows的efi应用,使Boot Menu界面上的Windows Boot Manager可以工作
| +--BCD............启动配置文件,用户编辑启动菜单以及默认的启动顺序等
|--Boot
+--bootx64.efi.......一个针对UEFI的统一efi应用,可以针对所有的系统。如果是32位系统,则是boota32.ef
引导流程
计算机加电
|
BIOS自检
|
UEFI固件启动
|
根据NVRAM下的BootOrder顺序加载启动设备
|
获取对应启动设备下第一个存有正确efi应用的Fat32格式分区并加载
|
读取efi应用信息,加载到BCD文件
|
读取BCD文件下的记录以加载系统,默认Windows10系统是加载C:\Windows\System32\winload.efi应用
|
接下来就交给系统服务了。这样子就完成了系统的启动过程
说明一下:
什么叫做根据NVRAM下的BootOrder顺序加载启动设备,这个里面有几个知识点
NVRAM(非易失性存储器) 是BIOS用于存储本计算机启动设备信息的载体,可以通过 bcdedit /enum firmware 来查看信息,参考 这个
BootOrder 顾名思义就是一个引导顺序,可以在BIOS下调节,比如先引导Windows Boot Manager还是先引导ATA HDD0这个设备
什么叫做获取对应启动设备下第一个存有正确efi应用的Fat32格式分区并加载?正常情况来说,一个硬盘分区仅有一个Fat32格式的EFI分区,并且往往是在第一个,但是当出现多了EFI分区那么UEFI固件将如何加载呢?对于首选启动已经设置为了Windows Boot Manager的情况下可以忽略,因为这个里面已经明确定义了加载哪块硬盘的哪个分区下哪个文件。当没有这个Windows Boot Manager项目而只能通过ATA HDDX下的分区查找时,经测试。会加载上可识别的拥有正确efi应用(位置: (EFI_Partition)\EFI\Boot\bootx64.efi )的第一个EFI分区,并根据efi应用的信息加载对应的BCD文件。
So,总结如下。可以没有 (EFI_Partition)\EFI\Boot\bootx64.efi ,也可以没有: (EFI_Partition)\EFI\Microsoft\Boot\bootmgfw.efi ,但是不能2个同时没有,存在 (EFI_Partition)\EFI\Boot\bootx64.efi 的情况下,可以在BIOS的Boot Menu界面选择ATA HDDX启动,存在 (EFI_Partition)\EFI\Microsoft\Boot\bootmgfw.efi 并设置正确的情况下,可以在BIOS的Boot Menu界面上选择 Windows Boot Manager启动。
说几个关于引导的命令
mountvol 用于加载分区,比如 mountvol K: /s 加载默认的EFI分区到K盘
bcdboot 用于修复efi文件,比如 bcdboot C:\Windows /l en-us 将同时修复 (EFI_Partition)\EFI\Boot\bootx64.efi 和 (EFI_Partition)\EFI\Microsoft\Boot\bootmgfw.efi 2个文件
bootrec 可用于重新创建BCD文件,比如 bootrec /rebulidbcd 会在默认的位置 (EFI_Partition)\EFI\Microsoft\Boot 重新生成识别到的系统的BCD文件
bcdedit 用于编辑BCD文件
如果安装了双系统,不小心把WIN系统的引导删除了怎么恢复:
需要有PE系统,没有可以自己制作一个,这里不展开了
进去PE系统后修复BCD,以U启通PE为例:进入安装界面,点击左下角修复计算机。依次点击:“疑难解答”,“高级选项”,“命令提示符”。进入CMD命令 接下来依次输入
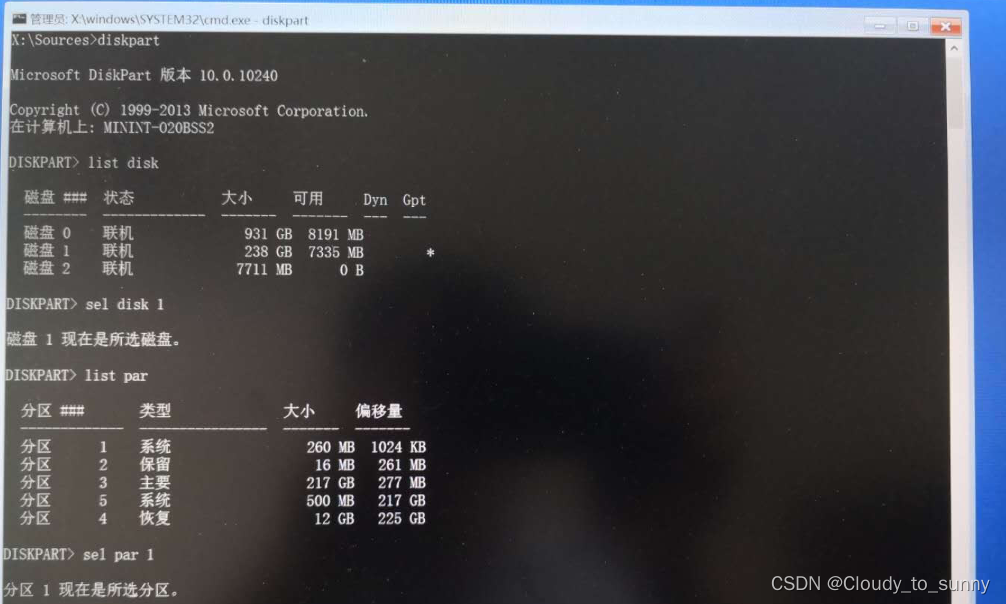
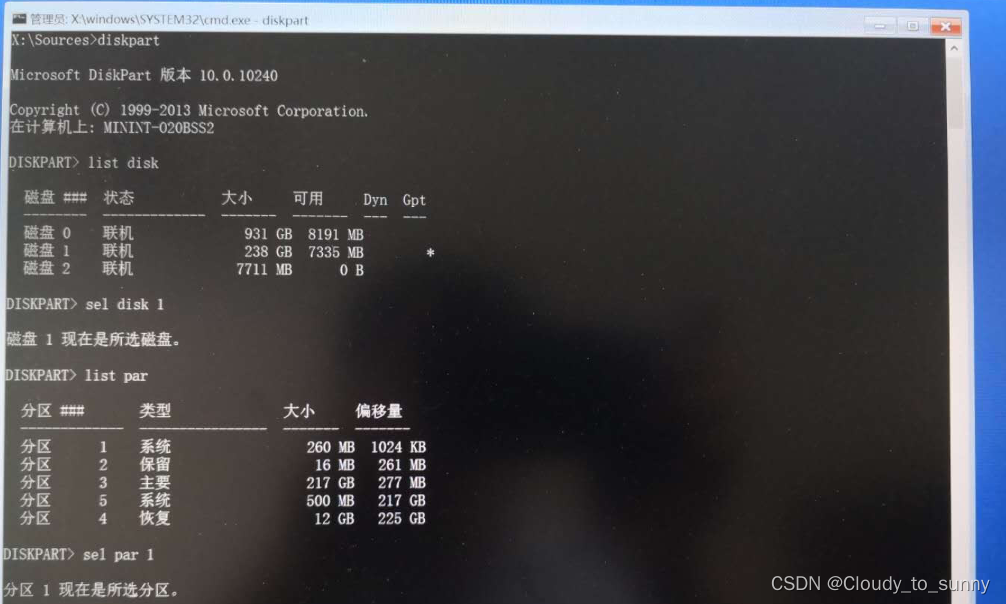
diskpart
list disk //列出所有挂在磁盘
sel disk X //选中刚刚自己发现的系统所在磁盘(X自己替换成数字)
list vol //查看磁盘里各个盘符,并确定自己的win系统所在的盘符(通常为C盘)
list par //列出上一步所选磁盘的分区,其中就有存放efi的分区,类型为系统,大小几百M
sel par x //选择efi的分区,x为分区编号
assign letter=o //为选择的分区分配一个盘符为o以便修复
exit //退出diskpart,不要关闭命令行框
bcdboot命令进行修复
命令行使用bcdboot命令,大概但不是下面这样
这里的c:\不一定是系统盘,需要用dir命令列出盘内文件来自己判断哪个才是系统盘,dir c:\ 和 dir d:\ 等,记住系统盘是哪个。

然后执行bcdboot命令:
最后输入
bcdboot x:\windows /s o: /f uefi /l zh-cn //其中x为亲自判断的系统盘盘符。
#盘符x:是你自己刚刚确定的盘符,最后的/l是小写的L,不是1
会提示“已成功创建启动文件”。
注意:有的电脑会显示“尝试复制启动文件失败”,如果以上输入没有问题,那么问题在于你的x盘不对,或者说再这个命令行里符号x不代表它。
如果显示“尝试复制启动文件失败”,输入exit退出diskpart并使用dir命令判断那个是系统盘。
然后输入exit退出命令行,关机重能进入弄丢的Windows了。
终于大功告成
小结
到目前为止是windows进去了但是我最初的目的还没达到阿,就是切换双系统。其实在这个折腾的过程中我已经解决了,下面来唠唠上面说的蠢的过程:
首先第一张图的系统选择页面是由ubuntu系统设置的开机引导页面供自己选择进入哪个系统,而我当时忘记了,所以就开始准备在windows系统里面准备设置开机引导来供选择进入哪个系统,最后没有成功还把windows搞得进不去了。原理上应该是可行了,两个系统之间的切换只需修改一个系统的开机引导选择就行了,而我已经在ubuntu里面设置了(具体设置可以参考这里),至于为什么没有开机的时候进入这个选择的页面是因为,BIOS里面把windows作为最先启动的了,所以以前开机直接就进windows了,没有出现选择的页面。当我把BIOS启动优先级改成了ubuntu最先启动,这时就会出现选择系统的页面了,然后选择就好了,就这么简单。